mirror of
https://github.com/bitcoin/bitcoin.git
synced 2026-06-10 14:48:46 +02:00
Merge bitcoin/bitcoin#22050: p2p: remove tor v2 support
5d82a57db4contrib: remove torv2 seed nodes (Jon Atack)5f7e086daccontrib: update generate-seeds.py to ignore torv2 addresses (Jon Atack)8be56f0f8ep2p, refactor: extract OnionToString() from CNetAddr::ToStringIp() (Jon Atack)5f9d3c09b4p2p: remove torv2 from CNetAddr::ToStringIP() (Jon Atack)3d39042144p2p: remove torv2 in SetIP() and ADDR_TORV2_SIZE constant (Jon Atack)cff5ec477ap2p: remove pre-addrv2 onions from SerializeV1Array() (Jon Atack)4192a74413p2p: ignore torv2-in-ipv6 addresses in SetLegacyIPv6() (Jon Atack)1d631e956fp2p: remove BIP155Network::TORV2 from GetBIP155Network() (Jon Atack)7d1769bc45p2p: remove torv2 from SetNetFromBIP155Network() (Jon Atack)eba9a94b9ffuzz: rename CNetAddr/CService deserialize targets (Jon Atack)c56a1c9b18p2p: drop onions from IsAddrV1Compatible(), no longer relay torv2 (Jon Atack)f8e94002fcp2p: remove torv2/ADDR_TORV2_SIZE from SetTor() (Jon Atack)0f1c58ae87test: update feature_proxy to torv3 (Jon Atack) Pull request description:  This patch removes support in Bitcoin Core for Tor v2 onions, which are already removed from the release of Tor 0.4.6. - no longer serialize/deserialize and relay Tor v2 addresses - ignore incoming Tor v2 addresses - remove Tor v2 addresses from the addrman and peers.dat on node launch - update generate-seeds.py to ignore Tor v2 addresses - remove Tor v2 hard-coded seeds Tested with tor-0.4.6.1-alpha (no v2 support) and 0.4.5.7 (v2 support). With the latest Tor (no v2 support), this removes all the warnings like those reported with current master in https://github.com/bitcoin/bitcoin/issues/21351 ``` <bitcoind debug log> Socks5() connect to […].onion:8333 failed: general failure <tor log> Invalid hostname [scrubbed]; rejecting ``` and the addrman no longer has Tor v2 addresses on launching bitcoind. ```rake $ ./src/bitcoin-cli -addrinfo { "addresses_known": { "ipv4": 44483, "ipv6": 8467, "torv2": 0, "torv3": 2296, "i2p": 6, "total": 55252 } } ``` After recompiling back to current master and restarting with either of the two Tor versions (0.4.5.7 or 0.4.6.1), -addrinfo initially returns 0 Tor v2 addresses and then begins finding them again. Ran nodes on this patch over the past week on mainnet/testnet/signet/regtest after building with DEBUG_ADDRMAN. Verified that this patch bootstraps an onlynet=onion node from the Tor v3 hardcoded fixed seeds on mainnet and testnet and connects to blocks and v3 onion peers: `rm ~/.bitcoin/testnet3/peers.dat ; ./src/bitcoind -testnet -dnsseed=0 -onlynet=onion` 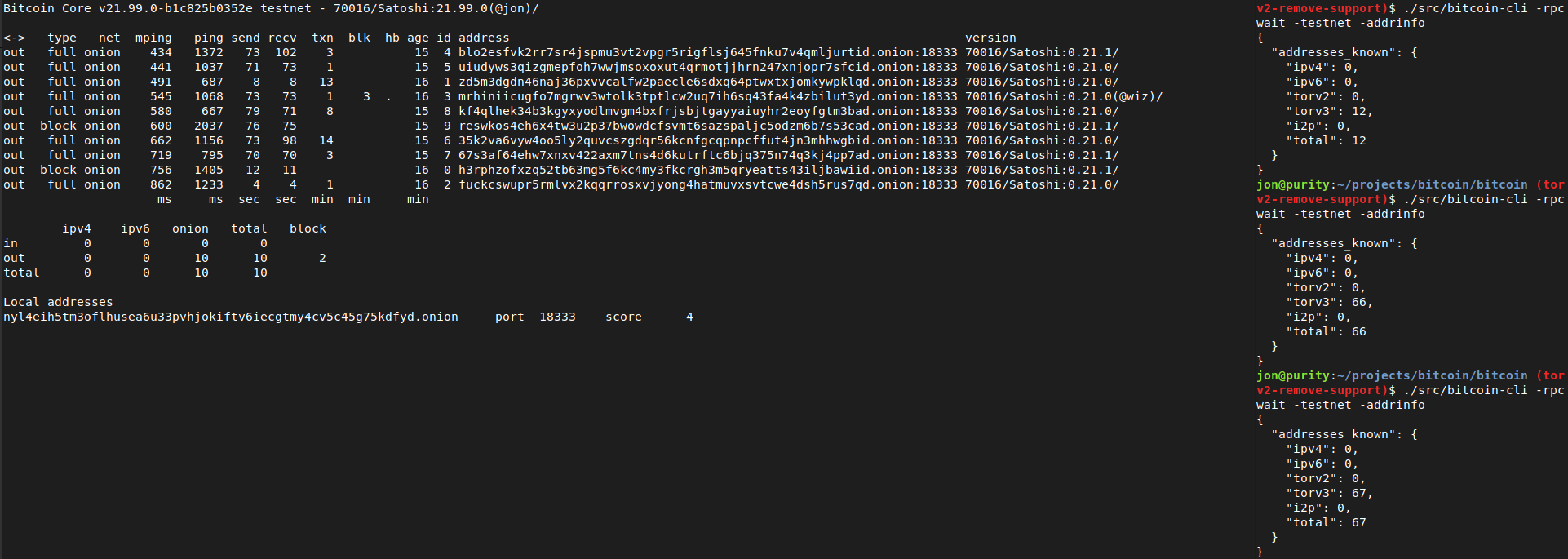 Tested using `addnode`, `getaddednodeinfo`,`addpeeraddress`, `disconnectnode` and `-addrinfo` that a currently valid, connectable Tor v2 peer can no longer be added:  Thanks to Vasil Dimov, Carl Dong, and Wladimir J. van der Laan for their work on BIP155 and Tor v3 that got us here. ACKs for top commit: laanwj: Code review ACK5d82a57db4Tree-SHA512: 590ff3d2f6ef682608596facb4b01f44fef69716d2ab3552ae1655aa225f4bf104f9ee08d6769abb9982a8031de93340df553279ce1f5023771f9f2b651178bb
This commit is contained in:
@@ -147,13 +147,13 @@ class ProxyTest(BitcoinTestFramework):
|
||||
self.network_test(node, addr, network=NET_IPV6)
|
||||
|
||||
if test_onion:
|
||||
addr = "bitcoinostk4e4re.onion:8333"
|
||||
addr = "pg6mmjiyjmcrsslvykfwnntlaru7p5svn6y2ymmju6nubxndf4pscryd.onion:8333"
|
||||
self.log.debug("Test: outgoing onion connection through node for address {}".format(addr))
|
||||
node.addnode(addr, "onetry")
|
||||
cmd = proxies[2].queue.get()
|
||||
assert isinstance(cmd, Socks5Command)
|
||||
assert_equal(cmd.atyp, AddressType.DOMAINNAME)
|
||||
assert_equal(cmd.addr, b"bitcoinostk4e4re.onion")
|
||||
assert_equal(cmd.addr, b"pg6mmjiyjmcrsslvykfwnntlaru7p5svn6y2ymmju6nubxndf4pscryd.onion")
|
||||
assert_equal(cmd.port, 8333)
|
||||
if not auth:
|
||||
assert_equal(cmd.username, None)
|
||||
|
||||
Reference in New Issue
Block a user